Startups must prioritize authentication to protect sensitive investor data. This guide summarizes Single Sign-On (SSO) and Security Assertion Markup Language (SAML), how they pair to simplify access, how to configure SAML, security best practices, and basic troubleshooting to preserve compliance.
Key Takeaways
- SSO lets users access multiple apps with one credential.
- SAML securely exchanges authentication data between identity and service providers.
- SSO + SAML reduce password reuse and login friction.
- Careful SAML configuration protects investor data rooms and supports compliance.
- Okta, OneLogin, and Microsoft Azure AD are common, compatible providers.
- Encryption, zero trust, and MFA strengthen enterprise login security.
- Common SAML errors are usually endpoint or certificate issues; check configs and logs.
- Regular testing and clear user communication keep access smooth.
What is Single Sign-On and How Does SAML Enhance Enterprise Login Security?
SSO allows a single authentication to grant access across multiple services. SAML transports signed authentication assertions between an identity provider (IdP) and a service provider (SP), enabling secure, repeated-free logins and reducing credential exposure—important for investor data rooms.
How do SSO and SAML protocols work together for secure access?
When a user requests access, they're redirected to the IdP to authenticate. The IdP returns a SAML assertion to the SP to confirm identity and attributes. The SP grants access based on that assertion, which improves security and usability.
Why are SSO and SAML critical for investor data room security?
Investor data rooms contain confidential documents. SSO with SAML provides central authentication, signed assertions, and encrypted transport, helping meet compliance and reducing risky password practices.
Clear SSO and SAML policies are vital for startups to sustain strong security and compliance, as research on single sign-on in growing startups indicates.
SSO and SAML Policy for Startups
Discusses authentication, single sign-on, and SAML. It uses Castor QISMS policy as an example of effective policy aligned with ISO requirements. Source: Single sign-on in a growing start-up, 2021.
How Can Startup Founders Configure SAML Authentication for Enterprise Login?
A structured SAML rollout reduces errors. Map responsibilities, gather IdP/SP metadata, and validate configuration before wide release.
A comprehensive roadmap can be invaluable for startups implementing SAML.
SAML SSO Implementation Roadmap for Startups
This thesis provides a roadmap for implementing a SAML 2.0 web browser SSO profile and focuses on the SAML SSO protocol. Source: A roadmap for ensuring SAML authentication using Identity Server for on-premises and cloud, 2019.
What are the essential steps to set up SAML with DealVue investor data rooms?
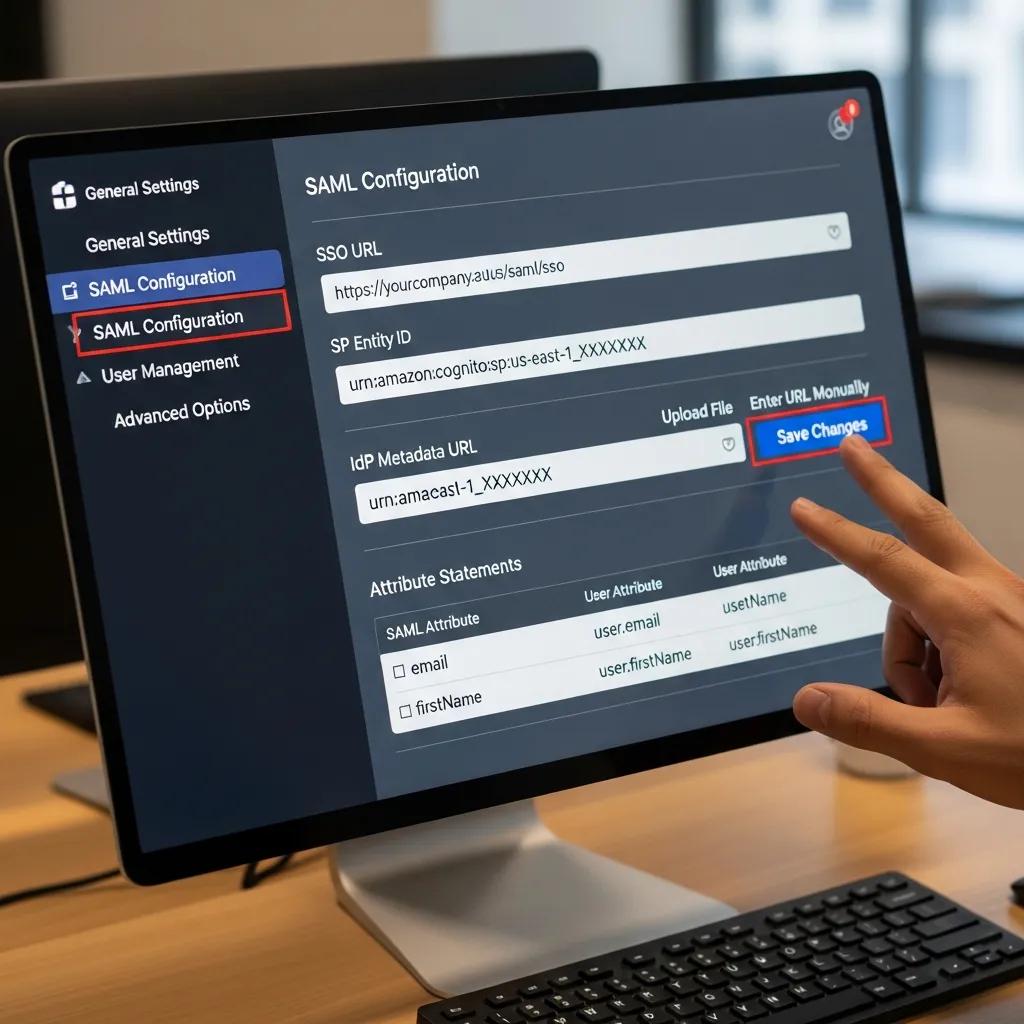
- Initial Setup: Choose a SAML-capable IdP and confirm compatibility with DealVue.
- Configuration Details: Enter DealVue's assertion consumer URL and entity ID into the IdP; import IdP metadata into DealVue.
- Testing the Setup: Test with staging accounts, verify attribute mappings, and confirm successful logins before production rollout.
These steps help founders implement SAML and strengthen investor data room access controls.
Which identity providers integrate seamlessly with DealVue’s SSO solution?
Common compatible providers include Okta, OneLogin, and Microsoft Azure AD; each offers mature SAML support and enterprise features.
- Okta: Robust security and a straightforward admin interface for startups.
Recent research highlights Okta’s effectiveness in integrating enterprise SSO and SAML with open-source tools.
Enterprise SSO & SAML Integration for Open-Source Tools
The Auth Shim pattern enables enterprise-grade SSO and automated RBAC for standalone OSS tools. A case study integrating a BI tool with Okta SAML demonstrates its effectiveness in streamlining access and enhancing security. Source: The Auth Shim: A Lightweight Architectural Pattern for Integrating Enterprise SSO with Standalone Open-Source Applications, Y Agrawal, 2025.
- OneLogin: Comprehensive identity management compatible with many apps.
- Microsoft Azure AD: Scalable SAML support commonly used in enterprise environments.
These providers support advanced authentication methods to protect investor data rooms.
What Security Best Practices Should Startups Follow for Investor Data Room Access?
Adopt layered controls: strong encryption, access logging, least privilege, and periodic audits to limit exposure and meet regulatory expectations.
How does encryption and compliance enhance enterprise login security?
Encrypt data in transit and at rest, use modern TLS and key management, and keep audit trails. Regular compliance reviews (e.g., GDPR/HIPAA where applicable) ensure controls remain effective.
What zero trust and multi-factor authentication strategies improve SSO security?

Implement zero trust principles: continuous verification, short-lived sessions, and contextual access. Enforce multi-factor authentication (MFA) to block credential-based breaches and limit lateral movement.
How to Troubleshoot Common Issues in Enterprise Login and SAML Configuration?
Most issues arise from configuration mismatches. Use systematic checks and logs to identify failures quickly.
What are frequent SAML setup errors and how to resolve them?
Typical problems are incorrect endpoints, mismatched entity IDs, and expired or wrong certificates. Verify both IdP and SP metadata, review SAML traces or logs, and confirm clock skew and certificate validity.
- Verify Configuration: Confirm URLs, entity IDs, and attribute mappings match on both sides.
- Check Logs: Inspect IdP/SP logs and SAML trace tools for assertion errors.
- Consult Documentation: Use provider and DealVue docs for specific error codes and remediation steps.
Systematic verification and logging speed resolution and reduce downtime.
How to ensure smooth investor access with DealVue’s enterprise login?
Prioritize UX and reliability: schedule regular tests, solicit user feedback, and publish clear login instructions and support channels.
- Regular Testing: Run periodic sign-in and role tests.
- User Feedback: Track issues and iterate on onboarding materials.
- Clear Communication: Provide step-by-step help and escalation paths.
These practices reduce support load and improve investor access.
Frequently Asked Questions
What are the benefits of using Single Sign-On (SSO) for startups?
SSO reduces password fatigue, centralizes access control, and simplifies onboarding/offboarding while supporting consistent security policies.
How can startups ensure compliance with data protection regulations when using SSO and SAML?
Audit authentication flows, encrypt data, retain access logs, and train staff. Update controls as regulations change and document processes for audits.
What role does multi-factor authentication (MFA) play in enhancing SSO security?
MFA adds an additional verification step (OTP, push, biometrics), significantly lowering the risk from stolen credentials.
What are the common challenges startups face when implementing SAML authentication?
Challenges include configuration errors, attribute mapping, and user adoption. Thorough testing and clear documentation reduce deployment friction.
How can startups maintain user satisfaction during the transition to SSO and SAML?
Communicate benefits, provide training and quick-reference guides, and collect feedback during the rollout to fix pain points fast.
What should startups do if they encounter SAML errors during configuration?
Check settings on both IdP and SP, review logs for assertions or certificate failures, consult vendor documentation, and contact support if needed.
Conclusion
SSO and SAML give startups a scalable way to secure logins and protect investor data. Use trusted IdPs, enforce MFA, follow a staged rollout, and maintain testing and monitoring to keep access secure and reliable.

![[background image] image of a healthcare professional using ai software](https://cdn.prod.website-files.com/6904eaa88b74b0aa55297314/69e1019ff7d741ae0032dc23_Screenshot%202026-04-16%20at%2011.30.30%E2%80%AFAM.webp)